Darkc0De
Privacy & Cookies: This site uses cookies. By continuing to use this website, you agree to their use. To find out more, including how to controlcookies, see. I have also included Word-list that come pre-installed with Backtrack and Kali called darkc0de and darkc0de. Darkcode Hacking Forum Forced Offline Darkode - a notorious hacking forum used by Lizard Squad and other cybercriminals - has been shut down. Is anyone having trouble with logging into darkc0de?. !download407407123258darkc0de150558. Credit. widgets Related Articles. widgets Contribution. This article is contributed.
No compression from darkc0de hashcobra -o create -a sha512 -c none -r darkc0de -d darkc0de # Crack 1a1dc91c907325c69271ddf0c944bc72 using darkc0de. Our technology has rummaged through the web and found several awesome security and hacking sites like Darkc0de. Come and check out darknet market avengers websites. Wpscan password brute forcer load darkc0de. How to hack cracking wpa2-psk passwords using aircrack-ng null byte wonderhowto. Cracking wpa wpa2 key with. But already a holding site, darkc0de, is live and advertising its new and improved services, showing you can't keep a dedicated hacker. Date, Notifier, H, M, R, L, Domain, OS, View. 2010/02/21, darkc0de-group, H, M,, Unknown, mirror. 2010/02/21, darkc0de-group. See Tweets about #darkc0de on Twitter. Working on my own darkc0de R. I. P #darkc0de #darkc0de - where the black code is in the front. I have also included Word-list that come pre-installed with Backtrack and Kali called darkc0de and darkc0de.
DarkC0de is a member of darknet market arrests Vimeo, the home for high quality videos and the people who love them. I'm trying to crack my friends wpa2 (were doing this together across the street) and I do not know how or where to get the darkc0de. Database Enumeration -MySQL v4 Data Extractor -MySQL v4 Table & Column Fuzzer Usage: darkc0de options -h help darkc0de. Darkc0de. version---------------------------. SELECT banner FROM vversion WHERE banner LIKE. Darkc0de 's profile image. By: darkc0de. May 11, 2016. Certifications, Salary Info for a Career in Penetration Testing - Cybrary. Greetz to all Darkc0de AH,ICW Memebers #Darkc0de-d3hydra,beenu,hubysoft,Gatyi, #Shoutz to,micro. These hacking dictionaries are already present o Kali Linux. So we can safely use it without download anything. RockYou (/usr/share/wordlists/.
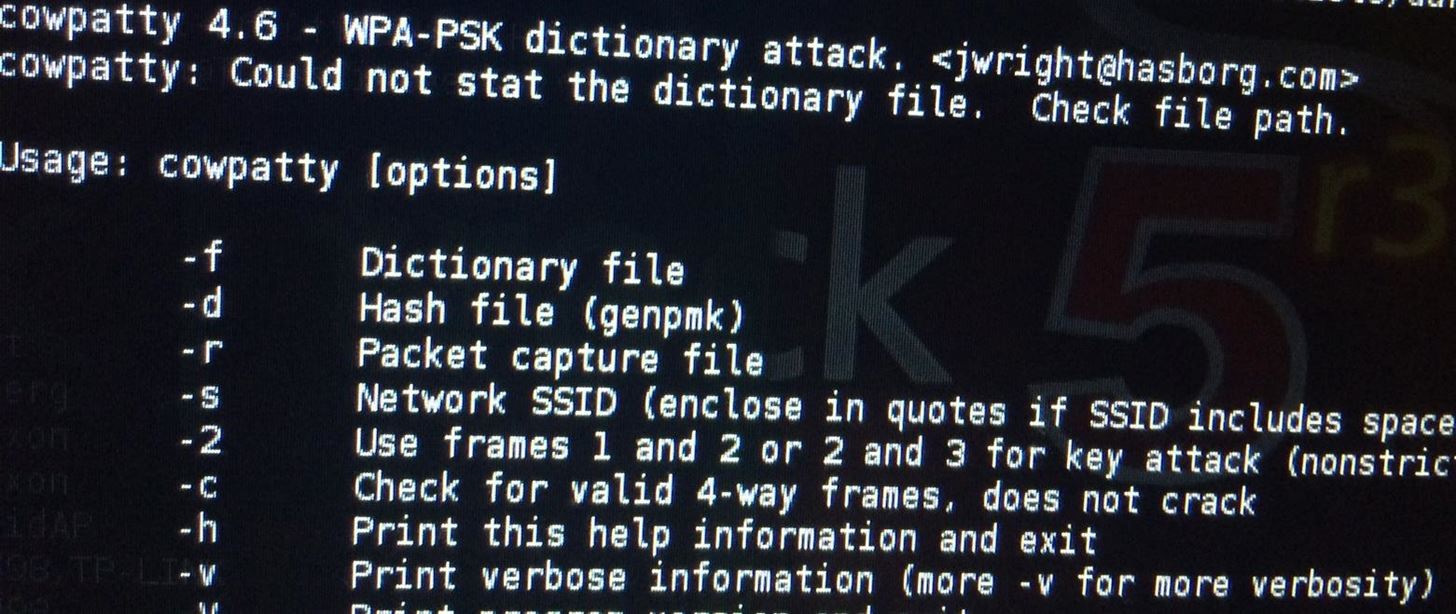
Android Security. Download Now Download. Download to read offline. Technology. Jun. 21, 2013. 540 views. android Security. Read more. darkC0de. Follow. E:\Izhar\Tool\SQL Injection\DarkCode Exploit>darkc0de -h From darkMySQLi URL, we can see this darkc0de will try to test SQL injection at null. Dark0de Reborn alternative links/Urls and availability status. I have also included Word-list that darknet links markets come pre-installed with Backtrack and Kali called darkc0de and darkc0de. Cowpatty -f darkc0de -r latesthackingnews -s ESSID of the wifi genpmk -f darkc0de -d pregendump -s ESSID of the wifi. Greetz to all Darkc0de AH,ICW Memebers #Darkc0de-d3hydra,beenu,hubysoft,Gatyi, #Shoutz to,micro. Load list of passwords from a file (RockYou/ darkc0de) and store it in a variable called pwdList. b. Loop through each password from pwdList.
Darkc0de options rsauron@gmaildotcom darkc0de Modes: Define: --dbs Shows all databases user has access too. Date, Notifier, H, M, R, L, Domain, OS, View. 2010/02/21, darkc0de-group, H, M,, Unknown, mirror. 2010/02/21, darkc0de-group. Darkc0de b4ltazar # Version : darkc0de # greetz for all members of ex darkc0de, darkc0de # import string, sys, time. Android Security. Download Now Download. Download to read offline. Technology. Jun. 21, 2013. 540 views. android Security. Read more. darkC0de. Follow. Darkc0de. Male US United darknet gun market States. Member Since April 2005. About Me: Hmmm... this person hasn't filled out the About Me section. Implement darkc0de-old-stuff with how-to, Q&A, fixes, code snippets. kandi ratings - Low support, No Bugs, No Vulnerabilities. Strong Copyleft License.
Torrents websites at the time of writing this, check out NordVPN of 1 month, government... As more people see how much money can be made, more opportunistic methods are being used. You can redistribute or modify it under the terms of the GNU Lesser General Public License as published by the Free Software Foundation. The Islamic State's rapid growth in power in the mid-2010s was facilitated by the terrorist group's embrace of all online channels available. Some sellers had decided to suspend activities during the crisis while others tried to stimulate sales darkc0de by offering discounts and lowering minimum order quantities. The Initial Coin Offering (ICO) is usually considered the public sale that allows smaller retail investors to participate, while private sales are usually reserved for large institutional investors such as venture capital (VC) firms to fund projects early on. Cyber Researchers Need to Predict, Not Merely Respond to, Cyberattacks: U. Despite operating in the dark web it maintains certain standards that are obligatory for both customers and sellers to provide a safe and trustworthy environment. It’s possible that the seizure of the DarkMarket servers may lead to a wave of arrests of online drug dealers and their customers if their addresses and identities are deciphered by police. Channel link updated June 23rd update, the previous channel was removed and a new channel link was updated accordingly. Typically, bots perform tasks that are both simple and structurally repetitive and at a much higher rate than possible for the human alone. We include extended discussions of the threat models and usage models that different schemes provide, and the trade-offs between the security properties offered and the communication characteristics different systems support.
Sellers primarily come from France, Germany, the UK, and the USA, and communications use encrypted messaging apps such darknet empire market as Wickr and Telegram. This means that you can’t visit the dark web websites or the darknet markets by simply running a Google search. Notify the website or app where you met the scammer, too.
Learn more:
- Versus Project Darknet Market
- Versus Project Market Darknet